HackTool.Win64.EDRSandBlast.D
2024年7月25日
:
Trojan.Win64.Hacktool (IKARUS)
平台:
Windows
总體(tǐ)风险等级:
潜在破坏:
潜在分(fēn)布:
感染次数:
信息暴露:


恶意软件类型:
Hacking Tool
有(yǒu)破坏性?:
没有(yǒu)
加密?:
没有(yǒu)
In the Wild:
是的
概要
感染途徑: 从互联网上下载, 下载了其他(tā)恶意软件
N
技(jì )术详细信息
文(wén)件大小(xiǎo): 443,904 bytes
报告日期: EXE
内存驻留: 没有(yǒu)
初始樣本接收日期: 2024年4月16日
Payload: 植入文(wén)件, 连接到 URL/Ip, 显示窗口
安(ān)装(zhuāng)
它添加下列进程:
- {Grayware File Path}\{Grayware File Name}.exe
植入例程
它植入下列文(wén)件:
- {Grayware File Path}\Ntoskrnl.pdb → deleted afterwards
- {Grayware File Path}\fltMgr.pdb → deleted afterwards
- {Grayware File Path}\wdigest.pdb → deleted afterwards
- {Grayware File Path}\WNBIOS.sys → vulnerable driver
其他(tā)详细信息
该程序执行以下操作(zuò):
- It employs techniques utilized to bypass EDR detections both in user and kernel mode.
- It performs the following actions to bypass EDR detections:
- Kernel Notify Routines Callbacks Removal → by exploiting an arbitrary kernel memory read/write primitive through exploiting a vulnerable driver
- Object Callbacks Removal → by disabling the Enabled flag in the OB_CALLBACK_ENTRY structure, unlinking the CallbackList of threads and process, or disabling object callbacks through disabling the SupportsObjectCallbacks bit in the ObjectTypeFlags field
- Minifilters' Callbacks Unlinking → by scanning structures used by the Windows Filter Manager to detect callback nodes containing monitoring functions and unlink them from their lists, making them temporarily invisible from the filter manager
- Disable ETW Microsoft-Windows-Threat-Intelligence Provider → by patching in kernel memory during runtime the ETW TI provider
- Userland Hooking Bypass → by either removing the hooks, using a custom or the existing EDR's trampoline to jump over and execute the rest of the function as is, using a duplicate DLL, or using direct syscall methods
- It detects EDR drivers and processes.
- It bypasses RunAsPPL by elevating its protection level higher than the LSASS process.
- It bypasses Credential Guard by enabling Wdigest to store cleartext credentials in LSASS memory.
- It downloads symbols from the Microsoft Symbol Server for the ntoskrnl.exe, fltmgr.sys, and wdigest.dll. If a corresponding *Offsets.csv file exists, it appends the acquired offsets from the symbols to the file.
- It connects to the following URL(s) to download symbols from the Microsoft Symbol Server:
- https://{BLOCKED}icrosoft.com/download/symbols/ntkrnlmp.pdb/2E37F962D699492CAAF3F9F4E9770B1D2/ntkrnlmp.pdb
- https://{BLOCKED}crosoft.com/download/symbols/fltMgr.pdb/BDB830D5AD37A0994727A90DE1D97BA41/fltMgr.pdb
- https://{BLOCKED}crosoft.com/download/symbols/wdigest.pdb/D0FEB1356A4987BF32419D0533E05AED1/wdigest.pdb
- It checks for the presence of the following files:
- {Grayware File Path}\NtoskrnlOffsets.csv → contains offsets used to perform Offsets Retrieval
- {Grayware File Path}\FltmgrOffsets.csv → contains offsets used to perform Offsets Retrieval
- {Grayware File Path}\WdigestOffsets.csv → contains offsets used to perform Offsets Retrieval
- It conducts offset retrieval to perform kernel monitoring bypass operations.
- It checks for the existence of the following service:
- Service Name: {8 Random Characters}
- If the service above is not found, it is then created with the following details and started subsequently:
- Name: {8 Random Characters}
- Display Name: {8 Random Characters}
- Type: Driver service
- Start Type: Auto start
- Binary Path: {Grayware File Path}\WNBIOS.sys
- It reverses its routines and deletes the installed service when the command "exit" is entered on its console.
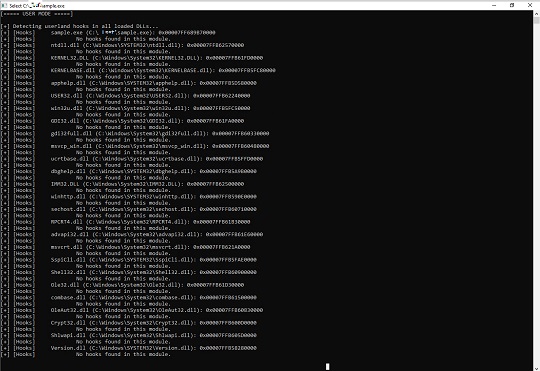
- It displays its logs on a console:
解决方案
最小(xiǎo)扫描引擎: 9.800
SSAPI样式文(wén)件: 2.747.00
SSAPI样式发布日期: 2024年7月25日
Step 1
对于Windows ME和XP用(yòng)户,在扫描前,请确认已禁用(yòng)系统还原功能(néng),才可(kě)全面扫描计算机。
Step 2
注意:在此恶意软件/间谍软件/灰色软件执行期间,并非所有(yǒu)文(wén)件、文(wén)件夹和注册表键值和项都会安(ān)装(zhuāng)到您的计算机上。这可(kě)能(néng)是由于不完整的安(ān)装(zhuāng)或其他(tā)操作(zuò)系统条件所致。如果您没有(yǒu)找到相同的文(wén)件/文(wén)件夹/注册表信息,请继续进行下一步操作(zuò)。
Step 3
重启进入安(ān)全模式
[ 更多(duō) ]
Step 4
删除该注册表键值
[ 更多(duō) ]
注意事项:错误编辑Windows注册表会导致不可(kě)挽回的系统故障。只有(yǒu)在您掌握后或在系统管理(lǐ)员的帮助下才能(néng)完成这步。或者,请先阅读Microsoft文(wén)章,然后再修改计算机注册表。
- In HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\{8 Random Characters}
Step 5
搜索和删除这些文(wén)件
[ 更多(duō) ]
有(yǒu)些组件文(wén)件可(kě)能(néng)是隐藏的。请确认在"高级选项"中(zhōng)已选中(zhōng)搜索隐藏文(wén)件和文(wén)件夹复选框,使查找结果包括所有(yǒu)隐藏文(wén)件和文(wén)件夹。 - {Grayware File Path}\ntoskrnl.pdb
- {Grayware File Path}\fltMgr.pdb
- {Grayware File Path}\wdigest.pdb
- {Grayware File Path}\WNBIOS.sys
- {Grayware File Path}\NtoskrnlOffsets.csv
- {Grayware File Path}\FltmgrOffsets.csv
- {Grayware File Path}\WdigestOffsets.csv
- {Grayware File Path}\ntoskrnl.pdb
- {Grayware File Path}\fltMgr.pdb
- {Grayware File Path}\wdigest.pdb
- {Grayware File Path}\WNBIOS.sys
- {Grayware File Path}\NtoskrnlOffsets.csv
- {Grayware File Path}\FltmgrOffsets.csv
- {Grayware File Path}\WdigestOffsets.csv
Step 6
重启进入正常模式,使用(yòng)亚信安(ān)全产(chǎn)品扫描计算机,检测HackTool.Win64.EDRSandBlast.D文(wén)件 如果检测到的文(wén)件已被亚信安(ān)全产(chǎn)品清除、删除或隔离,则无需采取进一步措施。可(kě)以选择直接删除隔离的文(wén)件。请参阅知识库页(yè)面了解详细信息。


