Ransom.Win32.SODINOKIBI.YABGC
N/A
Windows


恶意软件类型:
Ransomware
有(yǒu)破坏性?:
没有(yǒu)
加密?:
是的
In the Wild:
是的
概要
NIt arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites. 它可(kě)能(néng)是由其他(tā)恶意软件植入。
技(jì )术详细信息
新(xīn)病毒详细信息
它以文(wén)件的形式出现在系统中(zhōng),可(kě)能(néng)是其他(tā)恶意软件投放的,或者是用(yòng)户在访问恶意网站时无意中(zhōng)下载的。
它可(kě)能(néng)是由下列恶意软件植入:
安(ān)装(zhuāng)
它植入下列文(wén)件:
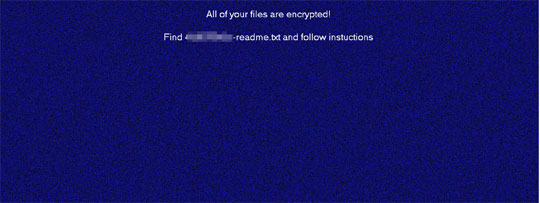
- %User Temp%\{Random Characters}.bmp → used as wallpaper
(注意: %User Temp% 是当前用(yòng)户的 Temp 文(wén)件夹。通常位于 C:\Documents and Settings\{user name}\Local Settings\Temp (Windows 2000(32-bit)、XP 和 Server 2003(32-bit))、C:\Users\{user name}\AppData\Local\Temp (Windows Vista、7、8、8.1、2008(64-bit)、2012(64-bit) 和 10(64-bit)。)
它添加下列进程:
- bcdedit /set {current} safeboot network → if -smode parameter is used (Restart the machine to Safe Mode with networking)
它添加下列互斥条目,确保一次只会运行一个副本:
- Global\{GUID}
其他(tā)系统修改
它添加下列注册表项:
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
Ed7 = {Hex Values}
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
QIeQ = {Hex Values}
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
96Ia6 = {Hex Values}
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
Ucr1RB = {Hex Values}
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
wJWsTYE = {Appended Extension}
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
JmfOBvhb = {Hex Values}
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\RunOnce
*AstraZeneca = %Windows%\MsMpEng.exe (or %User Temp%\MsMpEng.exe, depending on what was successfully ran) → if -smode parameter is used
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows\CurrentVersion\RunOnce
*MarineLePen = bcdedit /deletevalue {current} safeboot → if -smode parameter is used (Removes the machine from safe mode)
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
AutoAdminLogon = 1 → if -smode parameter is used
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
DefaultUserName = {current user's username} → if -smode parameter is used
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Winlogon
DefaultPassword = DTrump4ever → if -smode parameter is used
它通过修改下列注册表项,更改桌面壁纸:
HKEY_CURRENT_USER\Control Panel\Desktop
Wallpaper = %User Temp%\{Random Characters}.bmp
它将系统的桌面壁纸设置為(wèi)下列图像:
进程终止
它终止在受感染的系统上运行的下列服務(wù):
- backup
- memtas
- mepocs
- sophos
- sql
- svc$
- veeam
- vss
它终止在受感染的系统内存中(zhōng)运行的下列进程:
- agntsvc
- dbeng50
- dbsnmp
- encsvc
- excel
- firefox
- infopath
- isqlplussvc
- msaccess
- mspub
- mydesktopqos
- mydesktopservice
- ocautoupds
- ocomm
- ocssd
- onenote
- oracle
- outlook
- powerpnt
- sqbcoreservice
- sql
- steam
- synctime
- tbirdconfig
- thebat
- thunderbird
- visio
- winword
- wordpad
- xfssvccon
信息窃取
它收集下列数据:
- Computer name
- User name
- Workgroup
- Processor
- Operating System
- System Architecture
其他(tā)详细信息
它添加下列注册表键值:
HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
该程序执行以下操作(zuò):
- It will terminate itself if the affected system's keyboard layout is any of the following:
- Arabic - Syria
- Armenian Eastern
- Azeri Cyrillic
- Azeri Latin
- Belarusian
- Georgian
- Kazakh
- Kyrgyz Cyrillic
- Romanian-Moldova
- Russian
- Russian-Moldova
- Syriac
- Tajik
- Tatar
- Turkmen
- Ukranian
- Uzbek Cyrillic
- Uzbek Latin
- It wipes the contents of the following folder:
- backup
- It searches for files to encrypt in remote drives, fixed drives, removable drives, and network resources.
- It does the following if -smode parameter is used:
- It changes the current user's password to DTrump4ever
- It enables automatic logon
- It changes the default username to the current user's username
- It changes the default password to DTrump4ever
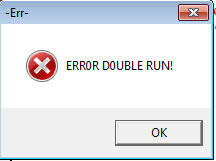
- It shows the following error message if 2 or more instances of itself is running:
解决方案
Step 1
对于Windows ME和XP用(yòng)户,在扫描前,请确认已禁用(yòng)系统还原功能(néng),才可(kě)全面扫描计算机。
Step 2
注意:在此恶意软件/间谍软件/灰色软件执行期间,并非所有(yǒu)文(wén)件、文(wén)件夹和注册表键值和项都会安(ān)装(zhuāng)到您的计算机上。这可(kě)能(néng)是由于不完整的安(ān)装(zhuāng)或其他(tā)操作(zuò)系统条件所致。如果您没有(yǒu)找到相同的文(wén)件/文(wén)件夹/注册表信息,请继续进行下一步操作(zuò)。
Step 3
重启进入安(ān)全模式
Step 4
删除该注册表值
注意事项:错误编辑Windows注册表会导致不可(kě)挽回的系统故障。只有(yǒu)在您掌握后或在系统管理(lǐ)员的帮助下才能(néng)完成这步。或者,请先阅读Microsoft文(wén)章,然后再修改计算机注册表。
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
- Ed7 = {Hex Values}
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
- QIeQ = {Hex Values}
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
- 96Ia6 = {Hex Values}
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
- Ucr1RB = {Hex Values}
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
- wJWsTYE = {Appended Extension}
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
- JmfOBvhb = {Hex Values}
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
- Windows\CurrentVersion\RunOnce
- *AstraZeneca = %Windows%\MsMpEng.exe (or %User Temp%\MsMpEng.exe)
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
- *MarineLePen = bcdedit /deletevalue {current} safeboot
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- AutoAdminLogon = 1 → if -smode parameter is used
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- DefaultUserName = {current user's username}
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon
- DefaultPassword = DTrump4ever → if -smode parameter is used
Step 5
删除该注册表键值
注意事项:错误编辑Windows注册表会导致不可(kě)挽回的系统故障。只有(yǒu)在您掌握后或在系统管理(lǐ)员的帮助下才能(néng)完成这步。或者,请先阅读Microsoft文(wén)章,然后再修改计算机注册表。
- HKEY_LOCAL_MACHINE\SOFTWARE\BlackLivesMatter
Step 6
搜索和删除该文(wén)件
- %User Temp%\{Random Characters}.bmp
- {Encrypted Directory}\{Appended Extension}-read.txt
Step 7
重置桌面壁纸
Step 8
重启进入正常模式,使用(yòng)亚信安(ān)全产(chǎn)品扫描计算机,检测Ransom.Win32.SODINOKIBI.YABGC文(wén)件 如果检测到的文(wén)件已被亚信安(ān)全产(chǎn)品清除、删除或隔离,则无需采取进一步措施。可(kě)以选择直接删除隔离的文(wén)件。请参阅知识库页(yè)面了解详细信息。
Step 9
从备份中(zhōng)恢复加密文(wén)件。